A Personal Blog
by Michael Froomkin
Laurie Silvers & Mitchell Rubenstein Distinguished Professor of Law
University of Miami School of Law
My Publications | e-mail
All opinions on this blog are those of the author(s) and not their employer(s) unelss otherwise specified.
Who Reads Discourse.net?
Readers describe themselves.
Please join in.Reader Map
Recent Comments
- Michael on Robot Law II is Now Available! (In Hardback)
- Mulalira Faisal Umar on Robot Law II is Now Available! (In Hardback)
- Michael on Vince Lago Campaign Has No Shame
- Just me on Vince Lago Campaign Has No Shame
- Jennifer Cummings on Are Coral Gables Police Cooperating with ICE?
Subscribe to Blog via Email
Join 51 other subscribers
Author Archives: Michael Froomkin
This Is Going to be Great
Posted in Uncategorized
Comments Off on This Is Going to be Great
A Strange Form of ORCID-Based … Advertising? Networking? Sp_mming?
My first thought was that this was a mistake.
My second thought was that this was an attempt to get me to read someone’s papers.
 On the gripping hand, having looked at the user’s ORCID record, which is for a Czech masters in economics who did some tutoring several years ago and claims ties to the United Kingdom, Malaysia, Solomon Islands, Georgia, and Armenia but doesn’t seem to publish….I have no idea.
On the gripping hand, having looked at the user’s ORCID record, which is for a Czech masters in economics who did some tutoring several years ago and claims ties to the United Kingdom, Malaysia, Solomon Islands, Georgia, and Armenia but doesn’t seem to publish….I have no idea.
Posted in Communications, Personal
Comments Off on A Strange Form of ORCID-Based … Advertising? Networking? Sp_mming?
Autoposting to Bluesky (continued)
 I’m still looking for a good tool to autopost to Bluesky. The Atproto Share plugin sends a link, but no more unless supplemented manually…
I’m still looking for a good tool to autopost to Bluesky. The Atproto Share plugin sends a link, but no more unless supplemented manually…
(I tried a manual supplement for this post)
Posted in Discourse.net
Comments Off on Autoposting to Bluesky (continued)
No Joke
There was a saying (which I first encountered 30+ years ago in the UK) that, “Everyone talks about the weather, but no one does anything about it.”
That silly joke has a much more ominous cast in light of global warming.
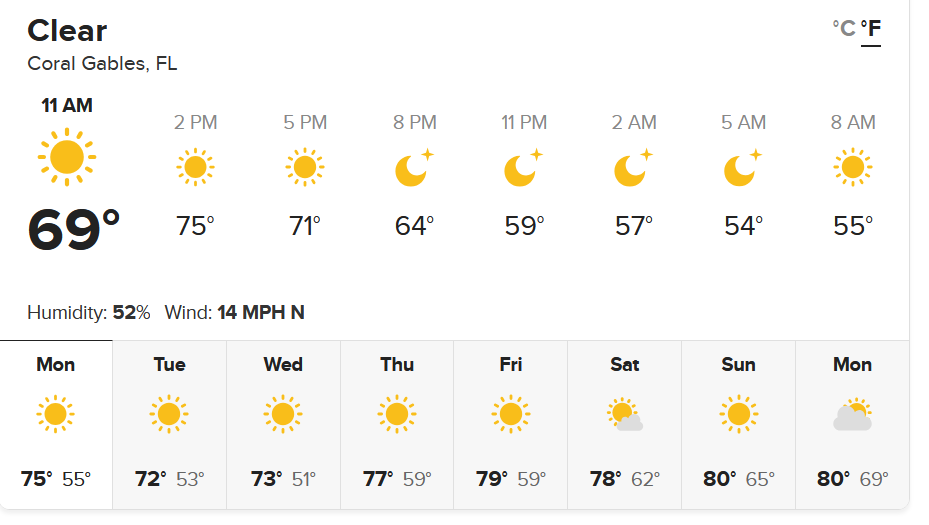
On a less grim note, it’s so cool here today I not only could open the windows but I put on a sweater! This is quite rare in South Florida.
On a technical note, this will be my first attempt to auto-post to Bluesky….
Posted in Coral Gables, Global Warming
2 Comments
David’s First TV Interview
My son the law professor made his TV interview debut yesterday.
I’m naturally biased, but I think he’s good at this.
Incidentally, the weird background is somewhere at a conference he was attending.
Posted in David Froomkin, Law: Constitutional Law
Comments Off on David’s First TV Interview
Election Day Anthem
If I had to bet it would be Harris, a Democratic House, and a Republican Senate. But I say that with no confidence.
Posted in 2024 Election
Comments Off on Election Day Anthem