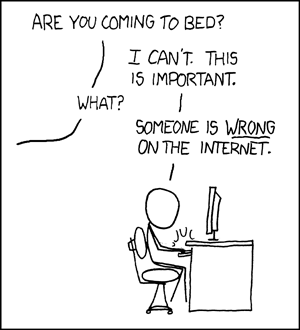
I know, I know, I have a case of this today:
…but forgive me.
There is a very serious error in the IT World posting Can you trust Chinese computer equipment?. I've written to the author to ask him to correct it, and to post the correction to Slashdot, which has repeated the error (which is how I came to find it).
The original item states,
Indeed, back in 1983, Ken Thompson, one the creators of Unix, admitted that he had included a backdoor in early Unix versions. Thompson's backdoor gave him access to every Unix system then in existence.
“Why am I always the last guy in the world to hear about this stuff?” I wondered. In this case, it is because it is not so. If you look at the actual article referenced, Ken Thompson's Reflections on Trusting Trust, his famous acceptance speech for the Turing Award, you will see it basically says the opposite of what the quote above suggests.
For starters, the very elegant backdoor attack presented in Ken Thompson's paper is a PROOF OF CONCEPT not an “admission” that anyone in fact did anything like it to early or late Unix builds. Ken Thompson in fact takes a very strong stand against such hacks. His point, though, is that the nature of compilers makes what have become known as “Thompson hack” or trusting trust attack very hard to detect.
It would be good if IT World ran a correction; if not maybe someone trying to chase down this latest piece of tin foil will find this posting instead.

You’re right, Thompson’s paper presents the hack as a proof-of-concept. And Thompson never said anything about releasing such a hack into the wild.
There are a couple of stories of him using it at specific targets. One was inside ATT, and “the compiler was never released outside.” It’s a secondary source:
http://personal.stevens.edu/~khockenb/ken_thomson_trojan_cc.txt
The other story has Thompson cracking the system at the Naval Postgraduate School by invitation. This anecdote is more widely circulated, but I couldn’t find any provenance for it. If it’s in a book, it must be true, right?
http://books.google.com/books?id=bv2n6o_6LaQC&pg=PA378&dq=%22ken+Thompson%22+compiler++(navy+OR+naval+OR+monterey)&cd=1
Still, going from “He wrote a paper describing a hack that he may have demonstrated on one or two systems,” to “He wrote a paper describing a hack that he deployed EVERYWHERE,” is quite a stretch.
The error might have a mathematical origin (TRUE once = TRUE everywhere). But I think it arises from storytelling: taking an awesome paper to its ultimate conclusion (well, penultimate — the ultimate conclusion is Ken Thompson taking over the world). But it’s still an error. Maybe a big one.
Wherever the error came from, sjvn repeats a rumor that Thompson admits to acts that:
* are possibly criminal
* expose Thompson and his employer to enormous liability claims
* are so unprofessional that Thompson might be rendered unemployable in his field.
When the source of the alleged admission is easily available on the web, does repeating the rumor constitute “reckless disregard” of the truth? IANAL, but someone here is …
It would be pretty awesome if someone took the occasion of his Turing Award lecture to admit to a felony, though, I have to say.
I first heard of it via the Jargon File (http://www.jargon.net/jargonfile/b/backdoor.html), but IMO whether or not KT released it is irrelevant; he told the story (and gave an example) so doubtless there are functionally identical bits of code in the wild, mostly by folks with a less deft touch (cf http://news.zdnet.co.uk/software/0,1000000121,39117696,00.htm)
This blog is very nice and informative. Entertaining is a pretty hard task but your post and experience serve and teach me how to handle and make it more simple and manageable.
Thanks for the tips Best regards.